In today’s world, oftentimes the threats that loom largest aren’t visible to the naked eye. Rather, they take the form of cyberattacks that endanger your data and, by extension, your revenue and reputation. In fact, over half of the businesses hit by cyberattacks this year lost over 5% of their total revenue, and 15% lost more than 10% after a single incident.
Given these stakes, many organizations have had to revisit their threat management strategy to ensure their cyber resilience. A thoughtful approach to threat management proactively protects your data and helps you respond quickly and effectively to any emerging attacks.
In this guide, we’ll break down everything you need to know about threat management.
Threat Management FAQs
What Is Threat Management?
Threat management is the framework that security professionals use to identify, assess, and mitigate cyber threats. The primary goal of threat management is to protect your organization’s IT infrastructure, data, and systems from bad actors.
Threat management focuses on continuous visibility and proactive defense. This enables your organization to identify and contain breaches faster; while the average time to detect and resolve a breach is currently about 241 days, actively monitoring anomalies and preparing to address emerging risks shrinks that window.
When integrated into a broader organizational resilience strategy, threat management ensures that operations can continue smoothly even when under attack, protecting your bottom line and brand reputation.
Who Needs Threat Management?
Any organization that handles sensitive data, relies on digital infrastructure, or provides critical services needs a threat management strategy. This includes healthcare providers safeguarding patient records, financial institutions protecting assets, government agencies securing classified intelligence, and private enterprises managing intellectual property. If your operations depend on connectivity, you are a target for cybercriminals.
How Is Threat Management Different from Vulnerability or Risk Management?
While these terms are often used interchangeably, they are in fact distinct:
- Vulnerability management is a cybersecurity-specific process that identifies and remediates gaps in your cyber resilience, including structural flaws and unpatched software.
- Threat management is also specific to cybersecurity. It is the continuous process of monitoring and defending against cybercriminals. Threat management is both proactive and reactive, focusing on minimizing the harm cyberthreats pose to your organization.
- Risk management is not specific to cybersecurity, encompassing the broader systematic process of identifying, evaluating, and mitigating risks to your physical assets or personnel.
Vulnerability and threat management are core pieces of a healthy risk management strategy. By incorporating these processes into your approach, you protect your organization from threats—cyber or otherwise—to ensure operational resilience and business continuity.
The Most Common Types of Cyber Threats
Awareness is a core tenet of threat management. Cyber criminals are constantly finding new ways to exploit vulnerabilities, often before cybersecurity teams even realize a gap exists. Ensure you understand the most common cyber threats that organizations face today, including:
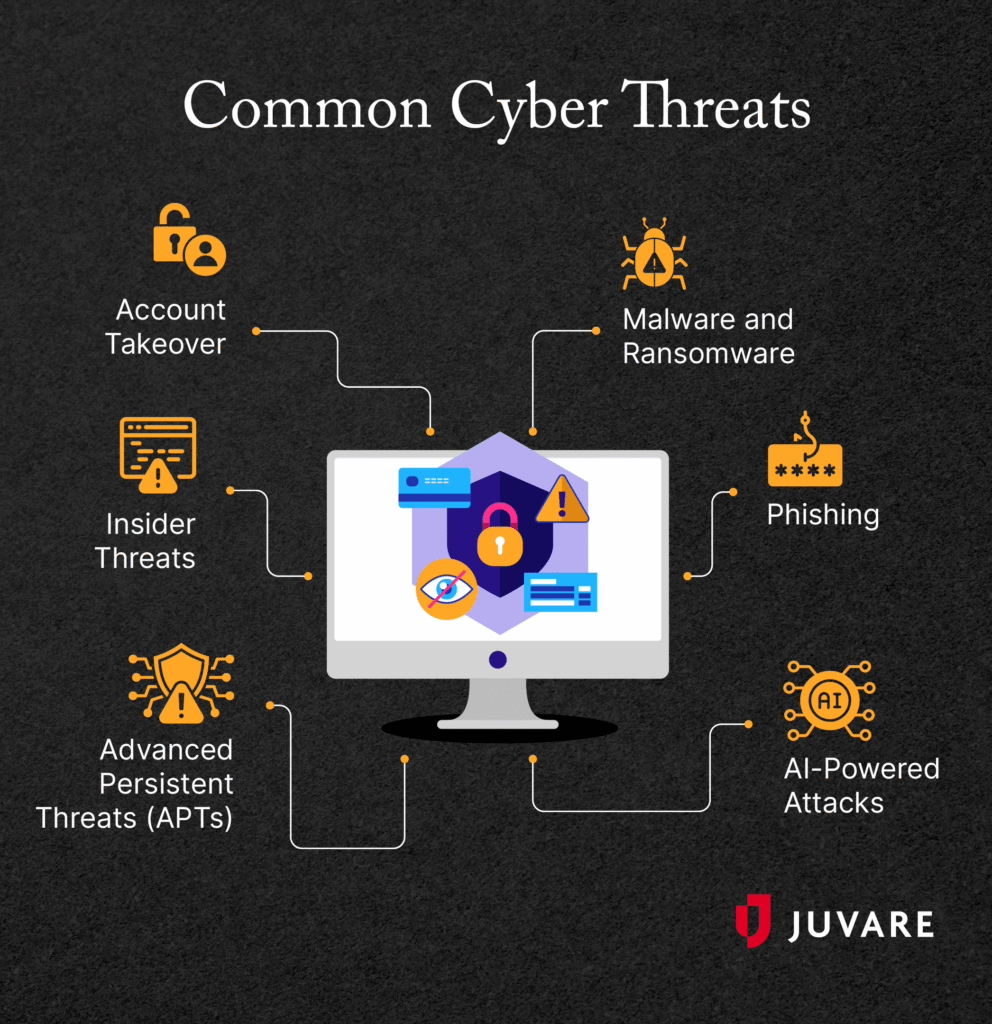
Malware and Ransomware
Malware is a portmanteau of “malicious” and “software.” These systems disrupt operations by stealing data, displaying ads, or damaging machines. Ransomware is a type of malware that holds data hostage in order to extort money.
Phishing
Phishing attacks impersonate your brand to send messages to your end-users. The goal is typically to steal users’ information or to trick them into downloading malware.
AI-Powered Attacks
A whopping 87% of organizations have seen an AI-driven cyberattack in the past year, and that number is only projected to grow. These attacks can take the form of automated phishing, agentic AI attacks that spot vulnerabilities faster than ever, and deepfake videos and audio personalized to trick end users.
Advanced Persistent Threats (APTs)
These are long-term, highly targeted attacks, often orchestrated by nation-state actors or well-funded criminal syndicates. Intruders establish a quiet foothold within a network to siphon data over months or even years.
Insider Threats
These risks originate from within your organization. Insider threats can be malicious (a disgruntled employee stealing data) or negligent (a well-meaning staff member accidentally clicking a phishing link or misconfiguring a database).
Account Takeover
Account takeover occurs when a bad actor uses stolen credentials to log into an online account. The goal of the hijacking might be to steal an individual’s identity, commit fraud, or steal data. Cybercriminals can gain access in a variety of ways, including through phishing schemes, purchasing login information on the dark web, or deploying bots that continuously test usernames and passwords.
While these threats are among the most common cyberattacks organizations face, keep in mind that this landscape is constantly changing. Adopting threat management software is more important than ever, especially as tech evolves to spot and exploit vulnerabilities in your digital infrastructure more quickly and effectively.
The Essential Phases of Threat Management
Many organizations structure their threat management approach in alignment with the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF). This globally recognized standard breaks defense down into five continuous phases:
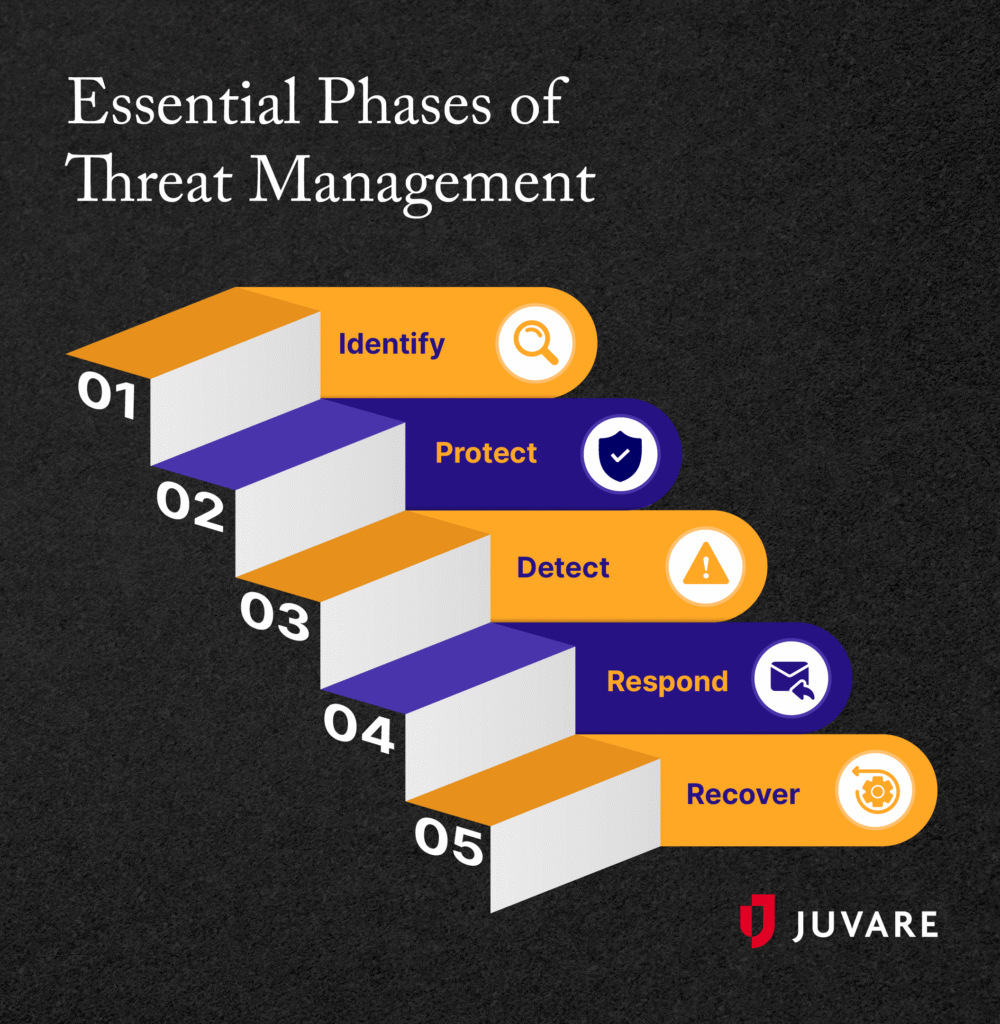
1. Identify
Before you can protect your assets, you must know what they are. This phase involves taking a comprehensive inventory of your organization’s physical devices, software platforms, and data flows. By establishing a baseline for your network, you can identify your vulnerabilities and prioritize your most critical assets.
2. Protect
This phase of threat management focuses on developing and implementing the appropriate safeguards to ensure the delivery of critical infrastructure services. Protection involves:
- Deploying access controls that prevent unauthorized users from using your tech and reduce internal confusion.
- Utilizing multi-factor authentication (MFA) to reduce the risk of account takeover.
- Encrypting data both at rest and in transit. At-rest data is stored on hard drives, in databases, or in the cloud and doesn’t move. In-transit data moves between systems, networks, or devices and is especially important to protect to preserve your collaboration capabilities.
- Maintaining strict patch management protocols to update software consistently to fix security vulnerabilities, in addition to resolving bugs and improving overall performance
3. Detect
Because no protective measure is 100% foolproof, your organization must have mechanisms in place to spot a breach as soon as possible. Use a threat intelligence platform with AI-empowered threat detection that continuously monitors global and internal data sources. Once an emerging risk is identified, your platform can activate multi-channel alerts.
4. Respond
Once you’ve detected a threat, it’s important to move quickly to minimize damage and protect your data. This phase of threat management covers the actions taken to contain the impact of an active cybersecurity event. Your team should execute a predefined incident response plan, isolating infected endpoints from the broader network, and communicating with internal and external stakeholders.
Use your threat intelligence platform to guide response, assign task ownership, track progress, and document decisions in a shared system of record, streamlining collaboration across teams and locations.
5. Recover
The final phase focuses on restoring capabilities or services impaired by a cyberattack. Recovery involves removing the threat entirely, restoring data from secure backups, and conducting a post-incident analysis to understand how the breach occurred and how to prevent it from happening again.
How Do You Determine Your Organization’s Threat Level?
Understanding your organization’s specific threat level requires evaluating both the attractiveness of your data to attackers and the maturity of your current defenses. Assess your environment against common vulnerabilities by answering the following questions to determine your risk profile:
Tips to Create a Threat Management Plan
Creating a formal threat management plan helps you ensure continuity of operations, no matter what cyber threat comes your way. With proactive planning, your organization will be ready to act when it matters most. To create a resilient threat management strategy:
Establish a Plan Proactively
Do not wait for a breach to figure out your response strategy. A proactive plan ensures rapid containment. Document a clear workflow that dictates how threats are escalated, who holds decision-making authority during a crisis, and how you will communicate with legal teams, PR, and law enforcement.
Conduct Regular Vulnerability Assessments
Threat management requires continuous auditing. Implement routine threat modeling to visualize how an attacker might navigate your specific network infrastructure. Additionally, empower your security teams to conduct proactive threat hunting by manually searching network logs and endpoints to uncover sophisticated threats that automated tools might have missed.
Offer Continuous Training
Human error remains one of the largest variables in cybersecurity. Conduct continuous, engaging security awareness training tailored to the threats your employees actually face. Run realistic phishing simulations and teach your staff to identify social engineering tactics that aim to trick them into divulging private information or downloading malware. This effectively turns your workforce into a primary line of defense.
Implement the Principle of Least Privilege
Ensure that employees and third-party vendors only have access to the data and systems absolutely necessary to perform their jobs. By restricting access, you limit the potential damage an attacker can do if they manage to compromise a single user’s account.
Foster a Culture of Security
Cybersecurity is not just an IT problem; it is an organizational imperative. Leadership must actively promote a culture that encourages and rewards reporting suspicious activity, rather than punishing it. When employees feel comfortable speaking up about a potential mistake, security teams can contain threats much faster.
How Threat Management Fits Into Your Risk Management Strategy
A truly resilient organization understands that cybersecurity breaches are often linked to broader operational consequences, and vice versa. Threat management should be a core pillar supporting your overarching risk management strategy.
For example, when a ransomware attack hits a hospital, it doesn’t just lock computer screens; it diverts ambulances and delays critical patient care. Alternatively, if a severe weather event takes a data center offline, the resulting digital downtime cascades into widespread supply chain disruptions.
A mature risk management plan accounts for this convergence, recognizing that the lines between cybersecurity, physical security, and personnel safety are indefinite.
To account for this overlap, you need to go beyond standard cybersecurity solutions. A comprehensive awareness, risk, and continuity suite connects contextualized threat intelligence directly to your specific facilities, assets, and personnel to protect the people and property connected to your digital systems as well as the systems themselves. By aggregating data across both digital and physical domains, you can:
- Correlate risks across domains: Automatically analyze how a digital disruption, severe weather event, or physical intrusion impacts your specific operational footprint.
- Mobilize the right people: Activate role-specific, multi-channel alerts to seamlessly coordinate an emergency response across IT, HR, legal, and facility management teams.
- Protect personnel: Provide mobile safety signaling to ensure workforce safety during compounding crises, keeping distributed or traveling teams connected.
Integrating threat management into a holistic risk strategy means your leadership team is prepared to handle any incident, whether the initial breach occurs in a cloud server or at the front door.
How Technology Aids Threat Management
A comprehensive threat management strategy requires advanced critical operations management solutions that help you identify risks earlier, mobilize teams faster, and coordinate emergency response.
At Juvare, we provide a wide range of tools and platforms to help public, private, and healthcare organizations prevent, withstand, and respond to cyber incidents:
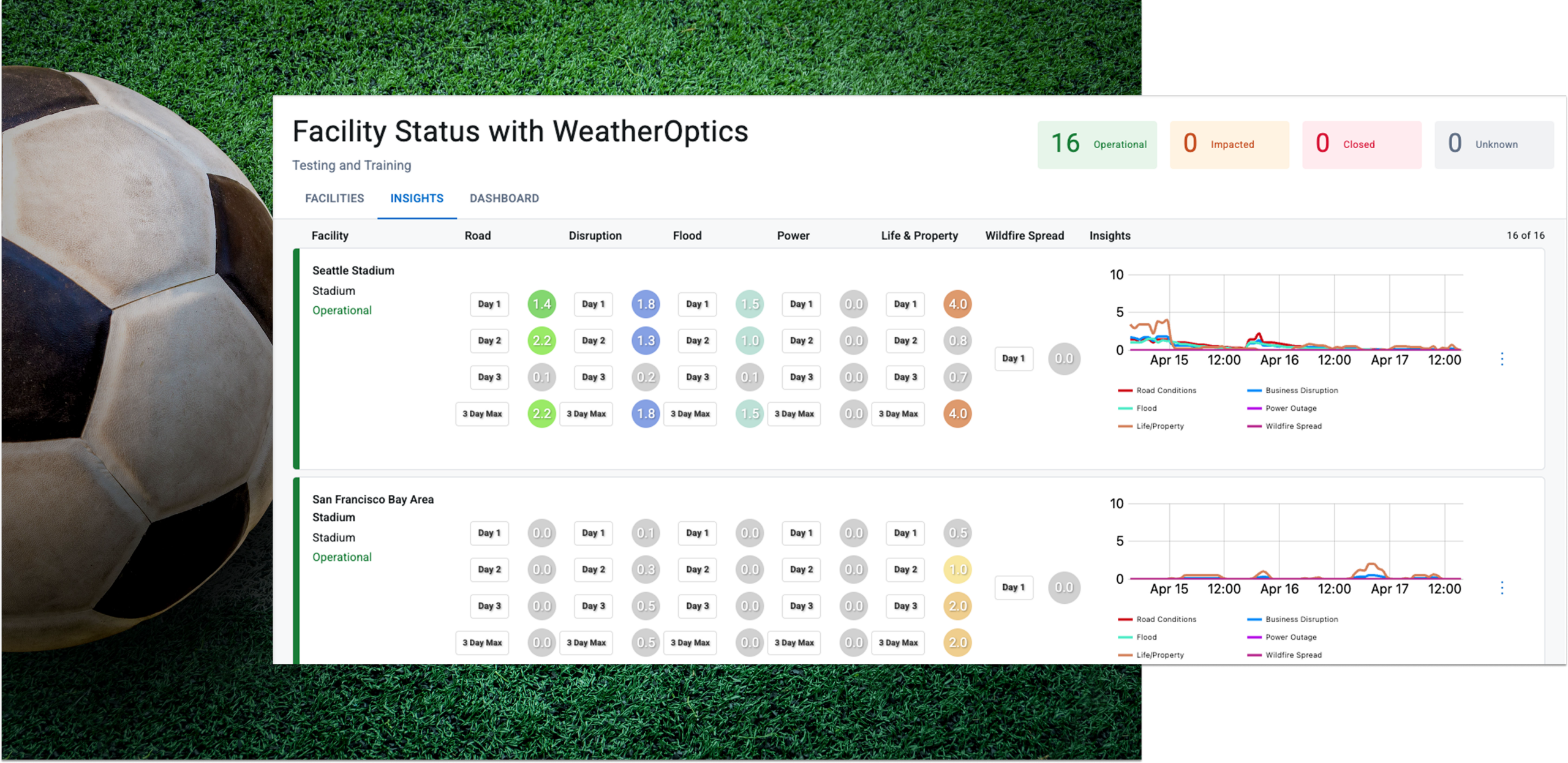
- Juvare ARC, our threat intelligence platform: Juvare ARC is a comprehensive threat detection and response solution that transforms raw data into operational threat intelligence. With real-time, AI-empowered intel, you can stay ahead of cyber threats. Juvare ARC will also help you respond to and recover from cyberattacks faster, thanks to multi-channel alerts and standardized workflows that enable clearer communication.
- WebEOC, Juvare’s continuity software: Private corporations and government agencies alike use WebEOC to enhance real-time situational awareness and decision-making. In the event of a cyberattack, WebEOC helps you quickly mobilize response efforts and coordinate across multiple departments.
- Crisis Track, Juvare’s damage assessment toolkit: Crisis Track’s disaster recovery capabilities allow you to monitor data integrity and operational impact in addition to damage to physical infrastructure. Quickly evaluate your situation and move towards recovery with automated workflows and reporting tools.
- UCP, Juvare’s federal government management software: Juvare’s United Command Platform (UCP) offers a real-time common operating picture across all domains, including land, air, sea, space, and cyber. Collaborate safely with key stakeholders using our FedRAMP High-certified tech.
Pairing a proactive, well-trained human workforce with robust incident management technology ensures that when a crisis strikes, your organization is prepared to respond, recover, and emerge stronger.
Additional Resources
To learn more about crisis preparedness and management, check out these resources:
- How to Build Cyber Resilience to Ensure Continuity: Building cyber resilience is integral to your organization’s continuity of operations. Explore the essentials of cyber resilience to prevent and respond to cyberattacks.
- The Future Is Now: Emergency Management’s Technological Modernization: Discover how technology is transforming the emergency management industry by speeding up processes, increasing the capacity for complexity, and improving coordination.
- How Situational Awareness Fuels Emergency Preparedness: Situational awareness helps organizations prepare for, respond to, and recover from crisis situations. Learn how a critical incident management platform helps.